Legal Tech has revolutionised efficiency – but it has also digitised the sacred trust between lawyer and client. This framework is your ethical firewall in a world where data breaches hit deeper than code.
Securing the Scales of Justice: A Data Protection Framework for Legal Tech Platforms
-

Syed Isa Alhabshee
-
-
Oct 29, 2025
-
12 min Read
-

The wood-panelled law library, with its rows of leather-bound books, is an image that still defines the legal profession. Yet, the reality of legal practice in 2025 is one of data streams, cloud platforms, and algorithms. E-discovery tools sift through millions of documents in hours, AI analyses contracts for risks, and virtual data rooms host the sensitive details of multi-billion-dollar mergers. This technological leap has brought incredible efficiency and expanded access to justice. But it has also digitised the very heart of legal practice: the confidential relationship between lawyer and client. The data flowing through these Legal Tech platforms is not just information. It is privileged communication, corporate strategy, and the personal details of people at their most vulnerable.
A data breach in this context is not just a technical failure; it is a catastrophic violation of the ethical duties that bind the profession. To survive and thrive, Legal Tech platforms need more than slick features. They need a data protection framework that serves as their digital professional oath. This is that framework.
The Framework: Pillars of Digital Legal Integrity
Pillar 1: Data Governance as the Digital Gavel
Effective data protection begins not with technology, but with authority and control. It is about establishing the rules of the digital court before the proceedings even begin.
First is the principle of absolute client data segregation. In the physical world, no lawyer would store files from competing clients in the same unlocked cabinet. The digital equivalent must be just as strict. A platform’s architecture must ensure that one client’s data is completely isolated from another’s, with no possibility of crossover.
Next comes a disciplined approach to purpose limitation and data minimisation. The temptation for any platform is to collect as much data as possible. This is a dangerous impulse. By just collecting the data strictly necessary for a specific legal matter, platforms dramatically reduce their risk profile. Anything more creates a honeypot of sensitive information that is both a liability and a target.
This control extends to user access. Granular, role-based access control (RBAC) ensures that a junior associate working on a discovery review cannot access the firm’s top-level M&A strategy documents. Finally, there must be a plan for secure data lifecycle management. A legal case has a beginning, a middle, and an end. The platform must provide tools for the secure and defensible deletion of data once its legal purpose is served, ensuring that old case files do not become future liabilities.
Pillar 2: The Fortified & Resilient Courthouse
With the rules of the court in place, we turn to the courthouse walls. Security cannot be an afterthought; it must be built into the very foundation. The non-negotiable standard for any sensitive legal data is end-to-end encryption (E2EE). This acts as an unbreakable digital seal on information, both while it is moving across networks and while it is sitting on a server. It ensures that only the authorised parties – the law firm and its client – can ever read the contents. Modern security demands a mindset shift, moving from a castle-and-moat approach to a Zero Trust architecture.
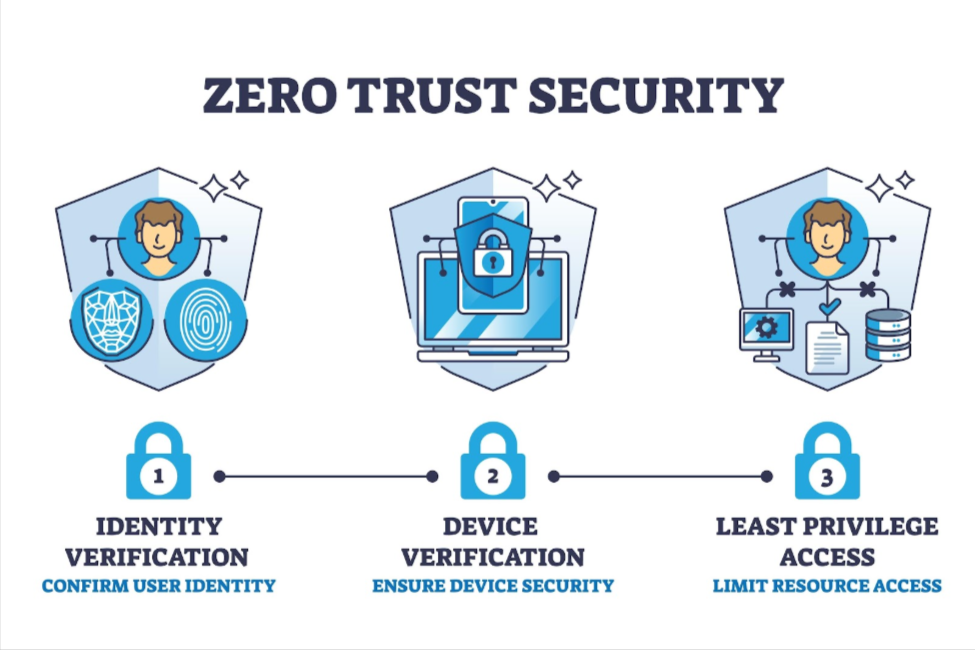
The principle is simple: never trust, always verify. Every single request to access data must be authenticated and authorised, regardless of whether it comes from outside the network or from a supposedly ‘trusted’ internal user.
The courthouse’s defences also depend on its suppliers. Vendor and supply chain due diligence is critical. A Legal Tech platform is only as secure as its own cloud provider or third-party API integrations. Rigorous vetting and robust contractual agreements are essential to maintain a secure chain of custody for client data.
But what happens when the walls are breached? That is right. It is no longer a matter of if, but when. A platform’s value is proven in its readiness. A clear, tested incident response and continuity plan is the difference between a managed crisis and a reputational collapse. This plan must cover everything from breach communication protocols to data recovery capabilities, giving law firms the confidence that the platform can withstand an attack and keep their operations running.
Pillar 3: Proactive Compliance & The Human Layer
Technology and process are two legs of the stool. The third, and often the most unpredictable, is the human layer.
Legal work is increasingly global, creating a dizzying maze of privacy laws. A platform must be built for this jurisdictional complexity, capable of handling the different rules for data residency and cross-border transfers under regulations like GDPR and, here in Singapore, the Personal Data Protection Act (PDPA).
This forward-looking approach is especially vital with the rise of ethical AI and data governance. As firms adopt AI for legal work, they need to ask tough questions. Is this tool trained on other firms’ privileged data? Can we explain its outputs to a court? Singapore’s work on frameworks like AI Verify provides a model for the world, pushing for transparency and accountability in automated systems. A platform’s AI governance policies are becoming as important as its security protocols.
Ultimately, the strongest defences can be undone by a single human error. The goal is to empower the human element with tools that make security the default. This means enforcing multi-factor authentication (MFA), providing clear audit logs so firms can monitor user activity, and designing intuitive interfaces that guide users away from risky behaviours. The platform has a responsibility to act as a digital guardrail for the busy professionals who rely on it.
Putting Platforms to the Test: Key Questions for Your Vendor
A framework is only as good as its implementation. For law firms conducting due diligence, the burden of proof lies with the vendor. Here are four critical questions to ask your current or prospective Legal Tech provider, drawn from the pillars above:
- On Governance: Can you describe, in technical detail, how our firm’s data is logically and physically segregated from other tenants, both at the application and database level?
- On Security: May we review a summary of your latest independent, third-party penetration test report and your SOC 2 Type II audit report?
- On Resilience: What are your guaranteed Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO) in the event of a major incident, and how are these documented in our service-level agreement?
- On AI: If your platform uses AI, is any of our data used for model training? If so, where is our explicit consent for this use documented?
A vendor’s ability to answer these questions with clarity, speed, and documentation is a powerful indicator of their maturity and commitment to securing your data.
Trust as the New Legal Tender
Building a Legal Tech platform worthy of the profession it serves requires a deep commitment to these three pillars: disciplined Governance, resilient Security, and a proactive approach to Compliance and the human layer.
In the digital practice of law, trust is the most valuable currency. For law firms choosing a platform, and for the platforms seeking their business, data protection is no longer just an IT issue or a compliance checkbox. It is a direct extension of a lawyer’s highest ethical duties. It is the new foundation for securing the scales of justice.
-

-
Syed Isa Alhabshee
Isa leads the Consulting and Legal team at Straits Interactive, managing legal affairs and data protection advisory services. A Certified Information Privacy Manager (CIPM), he has been conducting data protection and privacy training in Singapore since 2022. He holds advanced certifications in Data Protection Operational Excellence, Data Governance and Management, and Generative AI, Ethics and Data Protection, CIPM, CIPP/E and the Data Protection Practitioner Certificate (Singapore).



 +971 50 9295048
+971 50 9295048  +91 9746059514
+91 9746059514